About Mass Data
We are a Data Security Corporation that delivers high quality Product Evaluations and Data Security Support.
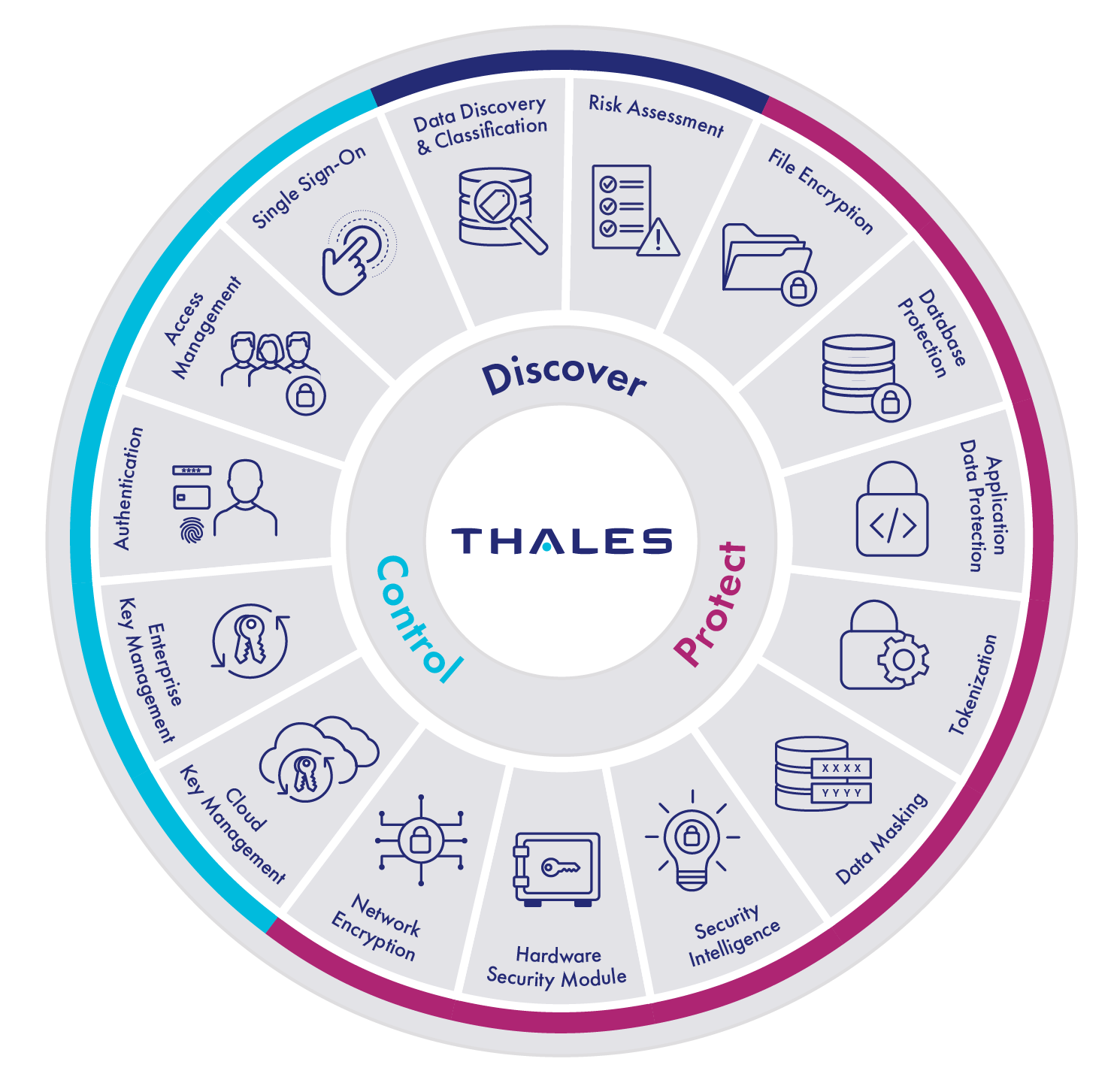
As a Thales Partner we specialize in helping you discover, deploy and manage the adoption of Thales Products.

Our focus is on decreasing the time it takes all Thales customers to evaluate and get the most out of their current or future Thales investments.
- Sensitive data requires encryption and external key management, especially in the cloud.
- All sensitive information shall be protected at rest and in transit.
- Data in use encryption will be used if and when available.
- All sensitive information shall be protected at rest and in transit.
- Data in use encryption will be used if and when available.
- Protecting you or your customers data shouldn’t be an afterthought.
- Your keys, certificates, and secrets should not be sprawled across your enterprise.
- Trust is the foundation of digital systems and so every transaction must be verified by identity.
- Hardware Security Modules are fundamental and required in every security program.
- Data in motion encryption between data centers should be able to handle 100Gbps.
- All clouds can be made safer, secure, private, and even sovereign with a little bit of tender, love, and care.
- People are the last line of defense.
RISE
- Respect
- Integrity
- Sovereignty
- Excellence
Our communities will come together and grow to craft thousands of secure digital foundations that make the world safer, secure, and private like it was meant to be.
To help over 10,000 organizations, data centers and clouds, to achieve digital sovereignty by 2030.
